PCI Compliance and Security
There is more to being a cashier than simply taking the payment…
PCI Announce DSS 4.0
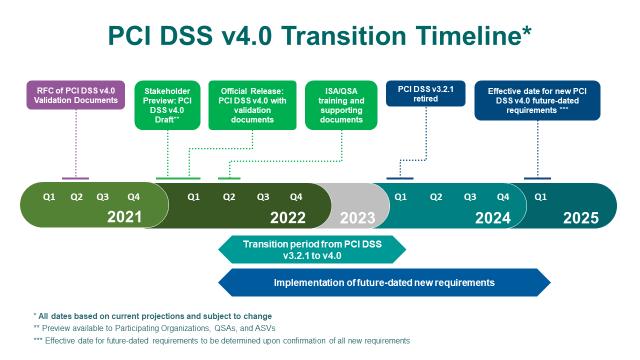
PCI DSS 4.0 is now published and replace PCI DSS 3.2.1 as of 31 of March 2022. Both versions of the standard will be active until retirement of v 3.2.1 on the 31st of March 2024 and v4.0 comes into effect at 31st March 2025. The transition period will allow organizations to become familiar with the new standard and develop towards implementation of the requirements in v4.0.
Important to note in the transition period is the assessment of compliance. The two versions cannot be mixed i.e., take one requirement from version 4.0 and others from version 3.2.1. If you do assessment based on version 4.0, this version must be used for the whole assessment.
The timeline for implementation as below (Source: PCI SSC)
Changes in PCI DSS related to compliance towards Requirement 9.9 at the Point of Sale is now replaced with Requirement 9.5. Point-of-interaction (POI) devices are protected from tampering and unauthorized substitution.
9.5.1 POI devices that capture payment card data via direct physical interaction with the payment card form factor are protected from tampering and unauthorized substitution, including the following:
- Maintaining a list of POI devices.
- Periodically inspecting POI devices to look for tampering or unauthorized substitution.
- Training personnel to be aware of suspicious behaviour and to report tampering or unauthorized substitution of devices.
Watch our two videos showing the importance of meeting PCI DSS Requirement 9.9 and the necessity of maintaining physical security at the point of sale – whether a fixed installation or a mobile payment application
Learn more about PCI Compliance and Security

SpacePole Payment solutions are proven, robust and follow the latest PCI-DSS physical security best-practice compliance requirements.
- Prevent theft or replacement with an unauthorised terminal
- Prevent data capture from the payment infrastructure
- Prevent the addition of skimming equipment to the terminal or network
- Protect PIN data that is vulnerable to shoulder surfing
- Protect unattended terminals and prevent physical removal
- Protect not only the terminal, but the cables as well
